The product launch was going smoothly.
- The roadmap was aligned with the launch.
Then, the product launch was stalled.
The roadblock was a compliance issue.
There were missing logging accesses. There was exposed sensitive data in a data pipeline. Engineering stopped shipping features to work on audit questions.
This is the reality for teams who don’t consider compliance until it’s too late.
In 2026, data infrastructure security is not only about protecting systems; it needs to be built to comply with the regulatory requirements by design.
If you are the CTO, or VP of Engineering, who is accountable for data infrastructure security, you are now enabling your business to function in a regulated market; you don’t just mitigate risk anymore.
6 Vendors to 1 Platform
Inside a 7-month consolidation that cut six tools to one and saved $1.4M.
You will learn:
- How to build safe, auditable and scalable systems via data infrastructure security
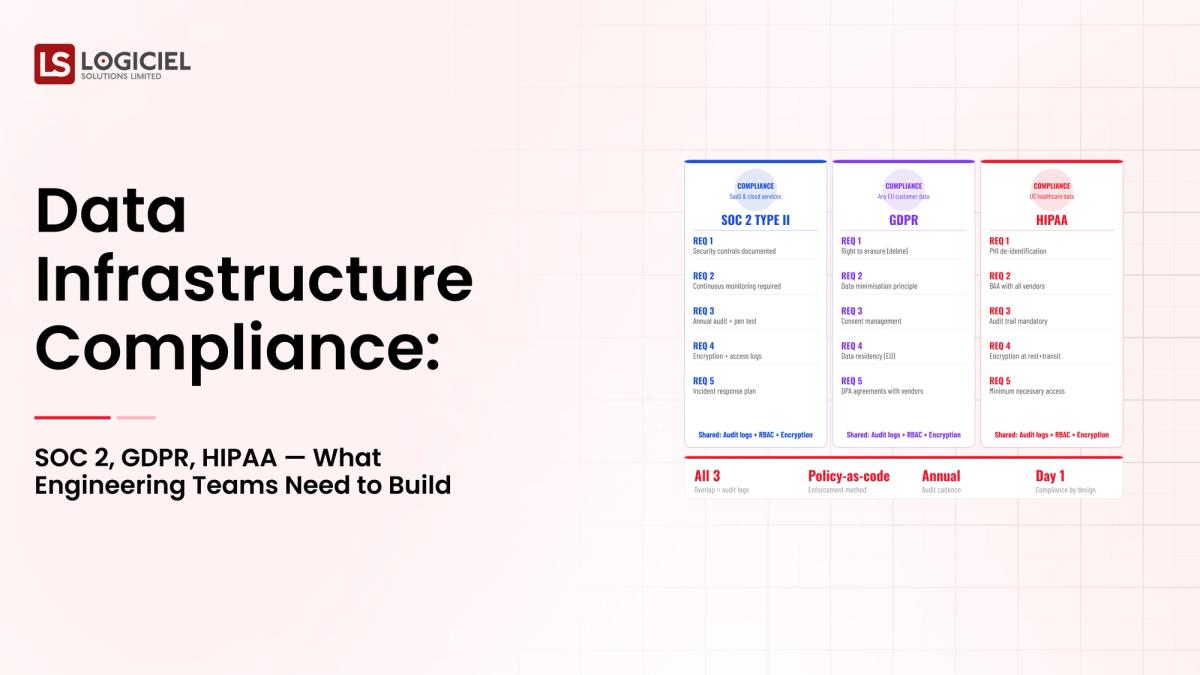
- How architecture assessment framework guidelines such as SOC 2, GDPR, and HIPAA dictate architectural decisions
- What does data infrastructure security actually mean (in real-world terms)
Let us provide you with the basics.
Section 1 - what is data infrastructure security?
A Simple Definition of Data Infrastructure Security
At its essence, data infrastructure security is comprised of:
- The systems, controls, and processes required to protect data from unauthorized access
- To ensure that data is handled in accordance with applicable regulations
- To be able to trace the data from its creation to the time it is disposed of from use
Data Infrastructure Example
A good way to think of your data infrastructure is as a secure building:
- Hallways of a building are the data pipelines
- Vaulted rooms of a building are the data storage
- Areas of a building that have restricted access are the access controls
- Cameras in a building represent the audit logs
If one part of the data infrastructure is weak, then there is an opening in the overall security of the data infrastructure.
Components of Data Infrastructure Security
A compliant data infrastructure security system consists of:
| Component | Function |
|---|---|
| Access Control | Controls who has access to what data |
| Encryption | Protects the data when it is at rest and during transport |
| Audit Logging | Records the access to the data and the changes to the data |
| Data Governance | Defines the policies and procedures that govern how the data will be protected |
Statistical Information Regarding Data Infrastructure Security
The failure to provide proper security for data increases the risk of:
- Data not being stored securely
- Violation of compliance requirements
- Business risk being increased
Compliance, security, operational stability, and trust can only result from providing proper security for data.
What Data Infrastructure Security Is Not
Data infrastructure security is not:
- Just having encryption
- Just having access control
- Just having a compliance check box
It's a design principle for the entire system.
Important Point to Remember:
- Security is not something that you can add after the fact
- Security must be built into each layer of the data infrastructure
Section 2: Data Infrastructure Security's Growing Importance in 2026
The importance of data infrastructure security will continue to grow exponentially.
Regulatory Pressure Is Growing
Organizations must meet specific compliance requirements, including, but not limited to:
- SOC 2 - for operational controls
- GDPR - for private data
- HIPAA - for healthcare
Noncompliance could result in:
- Financial penalties
- Legal ramifications - lawsuits - potential loss of client trust
Growing Data Volume and Sensitivity
Daily more and more systems are being built that are storing:
- Personal Data
- Financial Data
- Behavioral Data

This leads to increased risk exposure.
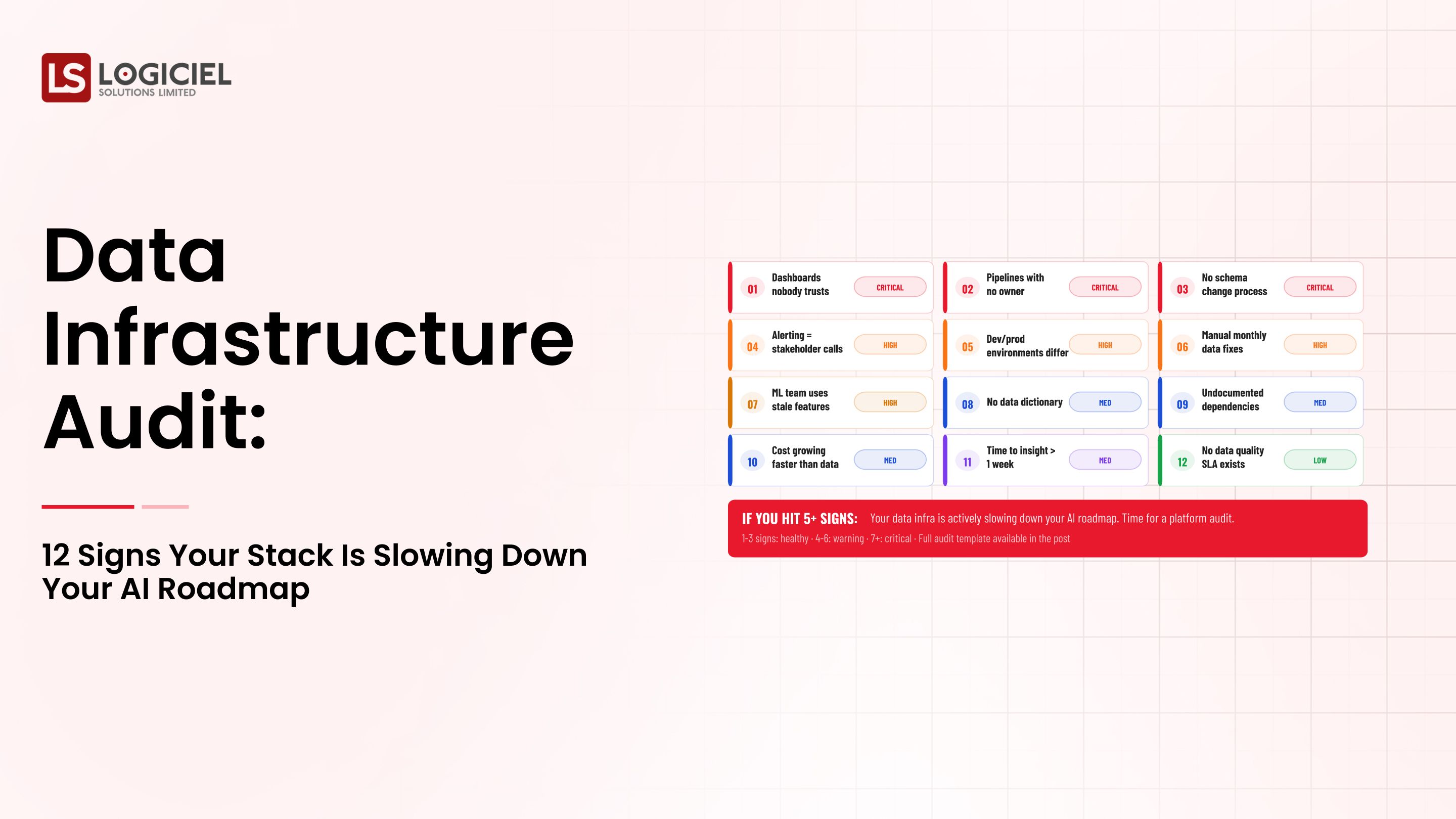
3. Risk Amplification from AI Schemes
AI systems:
- Take large amounts of data to work with
- Process sensitive types of data
If no proper processes exist:
- Leaking privacy of data becomes more frequent
- More frequent breaches of laws governing information privacy
4. Cost of Ignoring the Importance of Security
Without security in design, you will experience:
- Increasing frequency and volume of safety concerns
- Increasing cost in recovering from a breach
- Business operations being affected
Previous Safety Interventions:
- Reactive (waiting to see what happens)
- High incidence of incidents requiring removal
- High chance of an increase in future incidents
Post Safety Interventions:
- Proactive (putting safety measures in place)
- Having established levels of security (chart of who can see and how much)
- Lower chance of a future incident occurring
Key Idea
Security in today's world of technology is no longer a necessary restriction but rather a necessary business enabler.
Section 3: Core Essentials of Data Security Infrastructure: The Foundation of What You're Building
Definition of what you are building.
1. Access Control Layer
Who accesses logs, data logs outgoing invoices and their actions.
How to define permissions – using:
- Role based security with a specific predefined scope
- Using Fine Grained permissions
2. Encryption Layer
Data protection in two forms - at rest and in transit.
Mandatory encryption to establish you as compliant.
3. Audit Logging
Audit logs will track:
- Who accessed the data
- The timing and the types of changes that occurred
- What system activity occurred
Mandate you to perform either a compliance audit or if there is an incident.
4. Data Governance
- Governance Policies
- Definitions of data classifications
- Guidelines for the retention of all types of data
Consistent handling of all types of data.
5. Orchestration / Enforcement
The assignment of:
- Security policies
- Accessing rules
- Compliance checks across the pipeline
How the above elements create security of Data:
- Data is ingested
- Access of data is limited
- Data is encrypted
- Logging of Activity
- Enforcement of Corporation Policies
Commonly Misunderstood
Most teams focus solely on securing the storage of their data, when the truth is that secure Data Security Management also applies to both processing as well as the entirety of the data supply.
Key Point
What you're building is a system that has been designed to be secure rather than simply creating a system that Philosophical Principles.
Section 4: Real Life Examples of Implementing Data Protection Principles into Data Protection Systems
Let’s take a closer look at a practical example.
Use Case: Health Data Platform
A health company collects pours data from and back into the data warehouse and then to non-patient related systems including:
- Patient Records
- Billing
- Live Monitoring Data
Step-by-step process involved in implementing principles
1. Data ingestion
Management:
- The Data is delivered to the data warehouse
- Data is Validated and Categorised
2. Access Control
- Only those with the appropriate access are allowed to access the protected resources
- Also to maintain a record on access to the data
3. Encryption
- All Data is encrypted during its transfer
- Data is stored securely
4. Processing
- Transforming the Data into Business-Meaningful Data
- Policies have been established and enforced by the Engineers to prevent access to protected resources by those without appropriate access
5. Logging/Audit Logging
- Recording of Activity
- Determine who had accessed the Data
6. Serving
- APIs are provided
- Controlled Access to the APIs
What We Do Correctly
- Have strong access control
- Reliable log management
- Encrypt Data
What We Do Incorrectly
- Failure to write Audit Logs
- Improperly Configured Access Control
- Unencrypted Transfer of Data
Interaction with Engineers
Engineers create policies defining compliance, review logs of incidents and assist during incident.
Realisation
Security is not a separate entity operating outside of the company’s systems, it is integrated into every system within the company.
Section 5: Common Mistakes Data Security Teams Make
Even with the best Data Security Teams, there will be mistakes.
1. Using Compliance as the Goal
How some Data Security Teams ensure that they are complying with Government Regulations:
- Do only the minimum required to meet compliance
- Design and develop systems for future growth and development
2. Lack of funding for observability
An Example of Lack of Observability and/or Visibility:
- Incidents created
- Incidents exist but have not been reported
- Incidents are only discovered after compliance review
3. Data Contracts Missing
Changes can result in the flow of Sensitive Data and/or Incorrect Data.
4. Over-Engineering at the Beginning
More Complex Systems Require More Operational Support and Some What Slower to Development.
Security is Not a One-Time Job
An effective security program needs:
- Ongoing oversight
- Frequent modifications
The Most Important Point You Should Learn
The majority of security failures occur due to inadequate processes as opposed to technical shortcomings.
Part 6 - Best Practices Regarding Data Infrastructure Security - What Successful Teams Do Differently
Successful teams are proactive.
1. Build Security into Architecture
By:
- Developing their systems securely with an emphasis on creating a secure development lifecycle
- Using reusable components (and software development tools) instead of solely performing retrofitting of existing components or systems
2. Automate Compliance
They also automate:
- Monitoring and enforcing access control
- Utilizing audit logs to track system access and activity
3. Create Data Contracts
To:
- Ensure that the schema does not change unless there is a process to control the change
4. Invest in Observability
They monitor:
- The access to their data and how/when it is used
- Process activity within data processing pipelines
- Unusual or unexpected activity within data systems and processes
5. Regularly Conduct Audits
By:
- Evaluating their systems on a continuous basis
- Identifying any gaps that exist within their security processes
- Continuously improving security
6. Align Team Members
By including:
- People from engineering
- Individuals supporting the legal function
- Those responsible for compliance
The Key Insight
The leading teams incorporate compliance into their engineering processes as opposed to treating compliance as an additional requirement.
Reliability as Competitive Advantage
Inside a published-SLA program that turned silent reliability gains into a +42 NPS swing.
Call to Action
Today, security is not a "nice to have" but rather an essential and foundational element required to build robust, scalable, reliable, and compliant systems.
When comparing the difference between a reactive and proactive team, an organization can determine how the two teams approach data infrastructure security.
- Are they designing security into the architecture of their systems?
- Are they automating their compliance process?
- Do they consider data a regulated asset?
At Logiciel, we support engineering teams in designing secure, compliant data platforms that can assist them with future growth while reducing the associated risk.
If your organization's compliance-ready infrastructure has not been developed before you will succeed; but, as with anything before you take possession of it, it is only a matter of time until you encounter your first problem.
To learn more about how Logiciel's AI-first engineering teams can assist you with your goal of building a secure and compliant data infrastructure within your organization, please contact us.
Frequently Asked Questions
What Is Data Infrastructure Security?
Data infrastructure security focuses on protecting data and systems, providing compliance with applicable laws and regulations, and providing the ability to conduct "auditable" activity for all aspects of the data "lifecycle."
Why Is Compliance Important to Engineering Teams?
To stay within the law, to reduce risk, and to establish credibility and level of trust with customers and stakeholders. In certain industries such as medical, pharmaceutical, and governmental, compliance is vital for operational success.
What Are the Core Components of Data Infrastructure Security?
A: - Access Control - Encryption - Audit Logging - Data Governance - Enforcement Mechanisms
How Long Does It Take To Build A Compliance-Ready Infrastructure?
The ease of implementing your compliance-ready infrastructure depends on the complexity of your business. It may take 8 to 12 weeks from the beginning of implementing your compliance-ready infrastructure for you to have the core systems in place. Building toward your desired level of compliance can take an indefinite amount of time depending on the amount of continuous improvement you have within your processes.