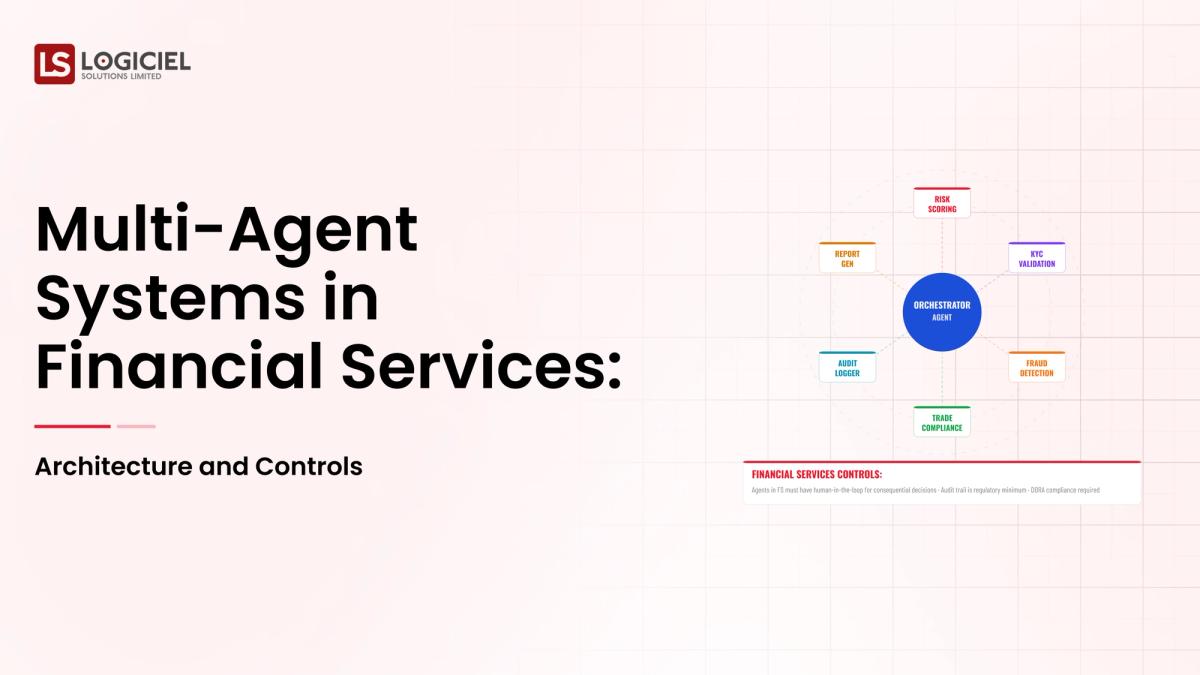
There is a financial services initiative deploying a multi-agent system across underwriting, fraud, and customer operations. The architecture diagram looks elegant; the regulator interview is in three weeks; the engineering team is reconstructing why each agent has a different audit trail format.
This is more than a delivery scramble. It is a failure of multi-agent architecture discipline.
A modern multi-agent system in financial services is more than coordinated agents. It is a designed combination of coordination shape, per-agent controls, shared audit trails, and an operating model that holds up under regulator review.
Real Estate Identity Resolution
Duplicate records are hiding your best leads. Identity resolution reveals true buyer intent and fixes your pipeline.
However, many programs design coordination first and discover the audit and control gaps when the regulator arrives.
If you are a Head of AI and are responsible for building or scaling your multi-agent AI program, the intent of this article is:
- Define what multi-agent architecture means in financial services
- Walk through coordination shapes and their tradeoffs
- Lay out the controls and audit trails that pass regulator review
To do that, let's start with the basics.
What Is Multi-Agent Systems? The Basic Definition
At a high level, a multi-agent system is multiple AI agents that coordinate to complete a workflow that no single agent could complete alone, with shared audit trails, controls, and operating models.
To compare:
If a single agent is a generalist contractor, a multi-agent system is a construction site with specialist trades. The coordination is the work; the safety inspection is the regulator.
Why Is Multi-Agent Systems Necessary?
Issues that Multi-Agent Systems addresses or resolves:
- Decomposing complex financial workflows into specialized agents
- Bounding blast radius through per-agent controls
- Producing the audit trail regulators expect
Resolved Issues by Multi-Agent Systems
- Provides explicit coordination patterns with documented tradeoffs
- Layers per-agent controls into a shared control plane
- Builds audit trails that survive regulator review
Core Components of Multi-Agent Systems
- Coordination shape (sequential, parallel, hierarchical, peer-to-peer)
- Per-agent tool surface and controls
- Shared audit trail across agents
- Cross-agent observability and incident response
- Operating model with regulator-aware on-call
Modern Multi-Agent Systems Tools
- LangGraph, CrewAI, AutoGen for multi-agent orchestration
- Anthropic Claude Code, OpenAI Swarm for managed multi-agent runtimes
- Shared audit-trail stores designed for regulator query
- Cross-agent observability platforms (LangSmith, Arize)
- Regulator-aware policy engines
Tooling supports the architecture; the discipline of regulator-aware design is the differentiator.
Other Core Issues They Will Solve
- Reduces incident severity through stronger blast-radius controls
- Improves auditability for financial services regulators
- Builds reusable patterns for the next multi-agent program
In Summary: Multi-agent systems in financial services are designed combinations of coordination, controls, and audit that pass regulator review.
Importance of Multi-Agent Systems in 2026
Multi-agent architecture matters in financial services because the workflows are high-blast and the regulator is watching. Four reasons.
1. Financial workflows decompose naturally into specialist roles.
Underwriting, fraud, compliance, customer operations. Multi-agent fits when the workflow asks for it.
2. Regulator expectations are specific.
Decision lineage, audit trails, evidence per action. Multi-agent without these protections is multi-agent without permission.
3. Blast radius compounds across agents.
A wrong action by one agent cascades; without per-agent controls, the cascade is hard to bound.
4. Operating-model maturity matters more than coordination cleverness.
The on-call rotation, runbooks, and tabletop exercises decide whether the system survives its first regulator visit.
Traditional vs. Modern Multi-Agent Systems Concepts
- Single-agent for simplicity vs. multi-agent for natural decomposition
- Per-agent audit trails vs. shared audit-trail design
- Generic on-call vs. regulator-aware on-call
- Coordination-first design vs. controls-and-audit-first design
In summary: Multi-agent architecture in financial services is a discipline; coordination is the visible part; controls and audit are the prize.
Details About the Core Components of Multi-Agent Systems: What Are You Designing?
Let's go through each layer.
1. Coordination Shape Layer
How agents communicate and pass work.
Shapes:
- Sequential: agents pass work in a chain
- Parallel: agents work concurrently and merge results
- Hierarchical: a controller agent orchestrates specialists
- Peer-to-peer: agents negotiate and decide together
2. Per-Agent Controls Layer
Each agent enforces its own controls.
Controls:
- Tool-level controls per agent
- Output validation per agent
- Per-agent kill switches
3. Shared Audit Trail Layer
Cross-agent decision lineage.
Audit components:
- Unified schema across agents
- Cross-agent decision lineage
- Queryable interface for regulators
4. Cross-Agent Observability Layer
Surfacing patterns and failures across the system.
Observability components:
- Per-agent telemetry stream
- Cross-agent correlation
- Cascade detection on failures
5. Operating Model Layer
Regulator-aware on-call and incident response.
Operating components:
- On-call rotation across engineering and risk
- Runbooks per multi-agent failure mode
- Tabletop exercises with the risk function

Benefits Gained from Per-Agent Controls and Shared Audit
- Bounded blast radius despite system complexity
- Defensible audit posture for regulators
- Faster incident response through cross-agent observability
How It All Works Together
Coordination shape decides how agents communicate. Per-agent controls bound blast radius. Shared audit trail captures decision lineage. Cross-agent observability surfaces patterns. Operating model handles incidents. Together, the layers turn coordination into a system that can be audited and operated.
Common Misconception
Multi-agent is just multiple agents working together.
Multi-agent is a designed system with coordination, controls, audit, observability, and operating model. Coordination is the visible part; the rest is what makes it operable.
Key Takeaway: Each layer addresses a specific risk. Programs that ship coordination without the other four layers ship audit failures.
Real-World Multi-Agent Systems in Action
Let's take a look at how multi-agent systems operates with a real-world example.
We worked with a financial services team designing a multi-agent system for fraud and underwriting workflows, with these constraints:
- Strict regulator review requirements
- Cross-team agent ownership across underwriting and fraud
- Audit trails that retain for seven years
Step 1: Decompose the Workflow into Specialist Roles
Identify roles that decompose cleanly; document boundaries.
- Per-role responsibility statement
- Per-role blast radius
- Coordination shape decision
Step 2: Design Per-Agent Controls
Tool surface, output validation, kill switches per agent.
- Per-agent tool spec
- Per-agent output validation
- Per-agent kill switches with documented criteria
Step 3: Design the Shared Audit Trail
Unified schema; cross-agent decision lineage; queryable interface.
- Unified audit schema
- Cross-agent lineage capture
- Regulator-ready query interface
Step 4: Build Cross-Agent Observability
Per-agent telemetry plus cross-agent correlation.
- Per-agent telemetry stream
- Cross-agent correlation rules
- Cascade detection on failures
Step 5: Design the Operating Model
Regulator-aware on-call, runbooks, tabletops.
- On-call rotation across engineering and risk
- Runbooks per multi-agent failure mode
- Annual tabletop with risk function
Where It Works Well
- Coordination shape matched to workflow
- Per-agent controls layered into shared control plane
- Audit trail designed before launch, not retrofitted
Where It Does Not Work Well
- Coordination-first design without controls and audit
- Per-agent audit trails without unification
- Generic on-call without regulator awareness
Key Takeaway: Multi-agent in financial services succeeds when the audit and control discipline equals the coordination cleverness.
Common Pitfalls
i) Premature multi-agent
Some workflows are single-agent problems dressed up as multi-agent. Decompose only when the workflow asks for it.
- Document why multi-agent is the right pattern
- Justify against single-agent baseline
- Reassess if coordination is dominating debug time
ii) Coordination-first design
Coordination is the visible part; controls and audit are what make the system operable. Design controls and audit alongside coordination.
iii) Per-agent audit trails without unification
Regulators need cross-agent decision lineage. Per-agent silos are insufficient.
iv) Generic on-call
Multi-agent failures cascade in ways single-agent failures do not. The on-call team needs multi-agent-aware runbooks.
Takeaway from these lessons: Most multi-agent failures in financial services are audit and control failures, not coordination failures. The audit and control work is the prize.
Multi-Agent Systems Best Practices: What High-Performing Teams Do Differently
1. Justify multi-agent against single-agent baseline
Multi-agent is a coordination overhead. Pay it when the workflow demands; avoid otherwise.
2. Design controls and audit alongside coordination
Controls and audit are not afterthoughts. They are co-equal layers.
3. Unify the audit trail across agents
Cross-agent decision lineage is what regulators need. Per-agent silos fail audit.
4. Build cross-agent observability
Cascades across agents are common; observability needs to detect them.
5. Tabletop with the risk function annually
Tabletops surface gaps that document review does not. Schedule annually; remediate findings.
Logiciel'svalue add is helping financial services teams design multi-agent architectures with coordination, controls, audit, and operating model that pass regulator review.
Takeaway for High-Performing Teams: High-performing financial services teams treat multi-agent design as a regulator-aware exercise. The audit trail is the test.
Signals You Are Designing Multi-Agent Systems Correctly
The signals below distinguish programs that are working from programs that look like they're working. Worth checking yours against the list.
The team describes failure modes without theater. They know the last three things that broke. They know why. They know what changed.
Cost is current. The dashboard shows yesterday's spend, broken out by feature, with someone whose job it is to explain it.
Change is unremarkable. Deploys ship, rollbacks happen, models swap, and nobody panics. Drama in production deploys is a sign that the system isn't yet running like infrastructure.
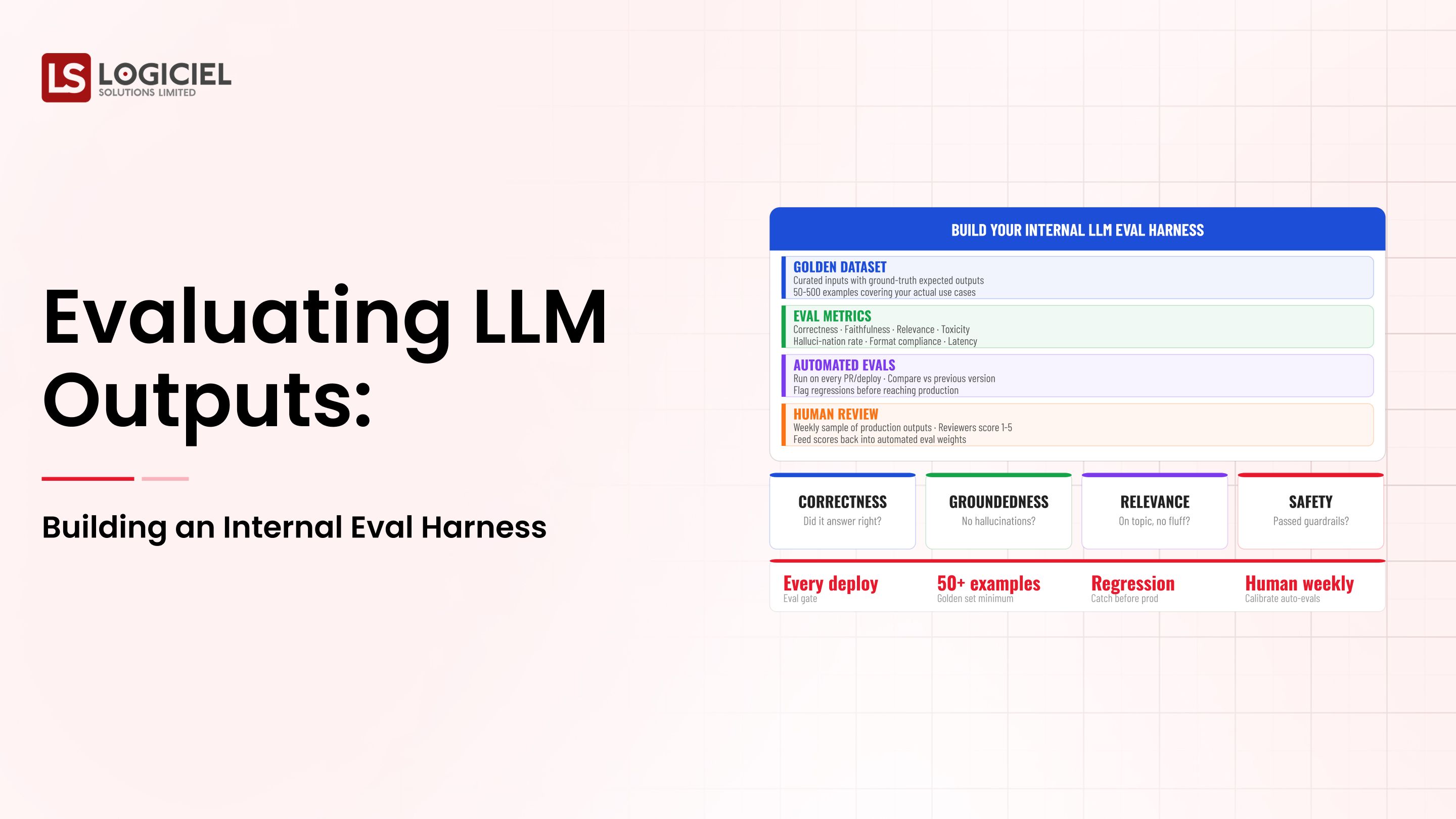
Eval runs continuously. Daily at minimum. Regression blocks deploy. Quality is a number on a screen, not an opinion in a meeting.
The team has done the lock-in math. The cost of removing each major dependency is documented in dollars and weeks. They didn't wait for the painful renewal to figure that out.
Adjacent Capabilities and Connected Work
Programs like this never run alone. They share infrastructure with the data platform, share alert noise with whatever observability stack the SRE team runs, and share a security review queue with everything else trying to ship that quarter.
They also share team capacity, which is the part that gets lost in planning. Platform engineering, applied ML, and SRE all carry pieces of this work. So does whatever leadership has marked as the next big AI initiative. Naming the overlap on day one prevents a year of "I thought your team had that."
If you take one thing from this section, take this: the integration with the data platform is your problem, not theirs. Same for the security review. Same for the on-call rotation. Treating those as someone else's job pushes work onto teams that didn't plan for it, and it comes back as a delay or an incident. Own what you depend on; partner where it makes sense; share the timeline.
Stakeholder Considerations and Communication
The same program will be evaluated by four or five audiences who don't share vocabulary. Worth getting ahead of.
Board questions: risk, ROI, competitive position. CFO: unit economics, forecast under multiple usage scenarios. CISO: threat model, audit defensibility. Engineering: scope, buy/build, on-call load. Line of business: when value lands, what users experience. None of these questions are unreasonable. They're just easy to fail when you're answering them in real time without prep.
The fix is boring but it works. Build a one-page brief for each major stakeholder. Update quarterly. Have it ready before the meeting where you need it. The cost of writing them is low; the cost of not having them is the meeting where the program loses its sponsor.
The communication cadence question is the same idea, applied to time. Weekly during delivery. Monthly during operation. Every incident, every meaningful change. The teams that protect the cadence keep their stakeholders. The teams that go silent between milestones surprise people, and surprises in this context are rarely good news.
Metrics That Tell You Multi-Agent Systems Is Working
Below the surface signals above are some operational metrics that are worth tracking weekly. They're not the metrics that make it into board decks. They're the ones that tell you, internally, whether the program is on the path or running in place.
Time from idea to production is the most useful single number. New use cases moving faster every quarter is the cleanest sign the platform is paying back. New use cases taking longer than they did six months ago is a sign that something has accreted that nobody is fixing.
Cost per unit of value is next. Spending less per output each quarter is the leading indicator that the platform layer is amortizing. Spending more is the leading indicator that you're carrying complexity nobody has audited.
Incident severity over time should trend downward. Operating models mature; runbooks improve; on-call gets better at triage. Flat severity is fine for a quarter; flat severity for a year says the team has stopped learning from incidents.
Reuse rate across programs is the metric most CTOs forget to track. What fraction of program one is in program two? In program three? High reuse is what compounds. Low reuse is what makes the second program as expensive as the first.
Stakeholder confidence is harder to measure but easier to feel. The proxies: budget approved, scope expanding rather than contracting, sponsor asking for more rather than asking you to defend. None of these are vanity. All of them tell you whether the program has runway.
Conclusion
Multi-agent systems in financial services succeed when audit and control discipline equals coordination cleverness. The regulator is the test; the layers are the design.
Key Takeaways:
- Multi-agent is a designed system with coordination, controls, audit, observability, operating model
- Justify multi-agent against single-agent baseline
- Audit trail must be unified across agents
When multi-agent is designed and operated correctly, the benefits compound:
- Bounded blast radius despite system complexity
- Defensible audit posture for regulators
- Faster incident response through cross-agent observability
- Reusable patterns for the next financial services agent program
Real Estate Investment AI
Your models aren’t wrong. Your data is. Here’s how real estate teams fix AI failures before they cost millions.
Call to Action
If you are designing multi-agent for financial services, the move this month is to design audit and controls alongside coordination.
Learn More Here:
- Agentic Systems Multi Agent Architectures Autonomous AI Engineering Teams
- AI Agent Development Services
- AI Agent Architecture Enterprise
At Logiciel Solutions, we work with financial services teams on multi-agent architecture, controls, and audit design that passes regulator review.
Explore how to design your multi-agent system.
Frequently Asked Questions
What is a multi-agent system?
Multiple AI agents that coordinate to complete a workflow that no single agent could complete alone, with shared audit trails, controls, and operating models.
When does multi-agent make sense?
When the workflow decomposes cleanly into specialist roles. Justify multi-agent against a single-agent baseline; coordination is overhead.
Which coordination shape should we use?
Sequential for chained workflows. Parallel for independent subtasks. Hierarchical for orchestrated specialists. Peer-to-peer for negotiated decisions. Pick based on the workflow.
How do we satisfy regulators?
Cross-agent unified audit trail, per-agent controls, designed observability, regulator-aware on-call. Plus tabletop exercises with the risk function annually.
What is the biggest mistake in multi-agent design?
Designing coordination first and discovering audit gaps later. Audit and controls are co-equal layers.