A compliance audit does not pass.
Your systems were not down, but your data did not meet your required business process standards as a required outcome of an audit.
Another possible outcome of a compliance audit that isn't passed is that your organization is unable to deliver on-time to its customers because engineers must wait an extended period of time for their access requests, thereby significantly impacting their productivity and weakening trust between the team and leadership regarding your organization's data infrastructure security model.
Budget Approval Playbook
Inside a 5-step framework that won $500K of infrastructure budget in 14 days.
For data leaders throughout the world, there is a challenge that all face today.
How do we create a secure data infrastructure that does not slow down teams?
CTOs and VPs of Engineering reading this guide will gain valuable insight into how to:
- Build a scalable access control strategy for your organization's modern data infrastructure security needs.
- Avoid making common mistakes that create bottlenecks or compliance risks when creating and implementing your organization's access control security policies.
- Develop and successfully deploy a phased in approach to access control security policies that balances security, speed and usability.
By 2026, access control will be more than just protection, it will also allow for a safe velocity increase.
Why Do Most Organizations Struggle With Effectively Managing Their Data Infrastructure Security?
The majority of organizations do not fail at access control because they ignore access to user data; theySome of the more common failure patterns include:
- Too strict control over access to data slows engineering teams down.
- Too much flexibility in granting access can be a major security risk.
This leads to:
- Engineers frustrated with the lack of timely access to production data.
- Exposure to compliance risk.
- Workarounds through the use of shadow access.
Why is it going to get worse in 2026?
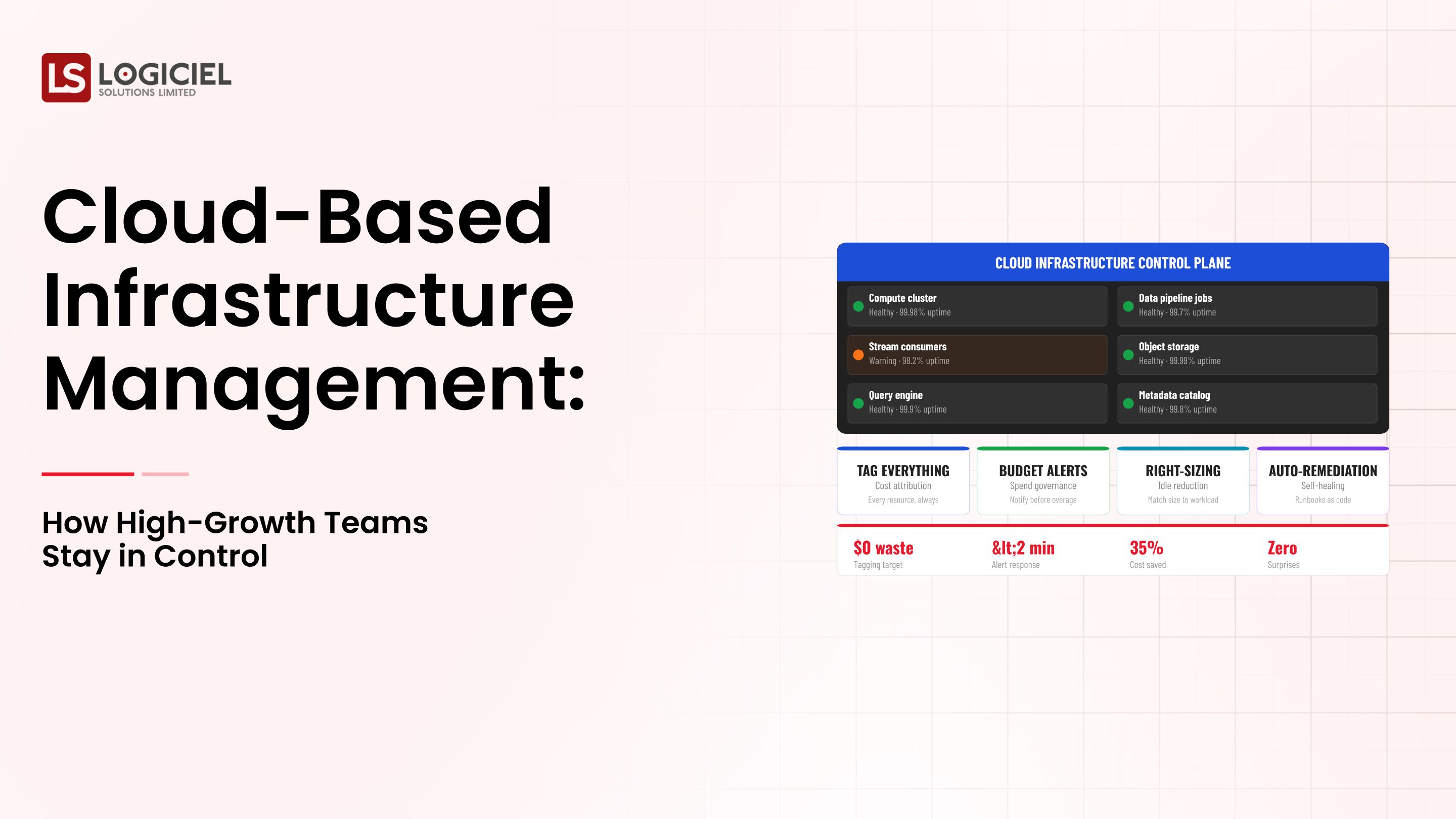
Today's modern security of data infrastructure must support:
- Distributed engineering teams.
- Cloud environments.
- Access to real-time data.
- Workloads for artificial intelligence and machine learning.
As a result, the size and number of users will continue to grow as will the number of ways to access data, leaving organizations even more vulnerable.
Example:
An analyst needs access to production data.
Took 3 days to get the request approved,
Missed the deadline,
Had to manually export production data from another source.
Now as a result:
- Data has been duplicated,
- Security has been compromised.
What success looks like.
Mature systems will grant access in a timely manner without compromising security.
Mature systems will keep a record and audit for every transaction.
Mature systems will require very little manual intervention.
Key Insight:
Data infrastructure security is about controlling access based on intelligence, rather than restricting access.
Prerequisites: What you must have in place prior to designing controls:
Before implementing access controls, there are several foundations that need to be in place.
1. Ownership Model
Clearly define:
- Owner - for each set of data
- Approver - for each access request
- Auditor - of access/use of the data
2. Baseline Infrastructure
The organization requires a functioning data platform, centralized identity management along with logging and monitoring.
3. Data Classification
The data should classify as:
- Sensitive data (i.e. PII/financial)
- Internal
- Public
This is an indication of what types of classification have access.
4. Stakeholder Alignment
All stakeholders (engineering/security/compliance) should agree to:
- Level of risk tolerance
- Access control policy
5. Metrics
Establish a process to track/measure

Step One: Audit Access Patterns
Create an Inventory of:
a. What data is accessed by whom
b. How often the data is accessed
c. Which systems the data is accessed through
Step Two: Identify Key Data Gaps
Most organizations have discovered the following:
a. Over-Permissioning: Too many individuals have access to data that they do not need.
b. Manual Processes: Access requests and approvals are slow and inconsistent.
c. Lack of Visibility: There is no clear trail of who has accessed what data.
Step Three: Map Data Flows
Identify:
a. Where sensitive data is flowing.
b. Who is accessing the data.
Step Four: Prioritize Patches/Fixes
Concentrate efforts on:
a. High-Risk Data.
b. Critical Paths.
Deliverable:
A prioritized list of:
c. Immediate Risks.
d. Long-Term Improvements.
Key Insight:
In order to secure access, you must first understand how that access is being used.
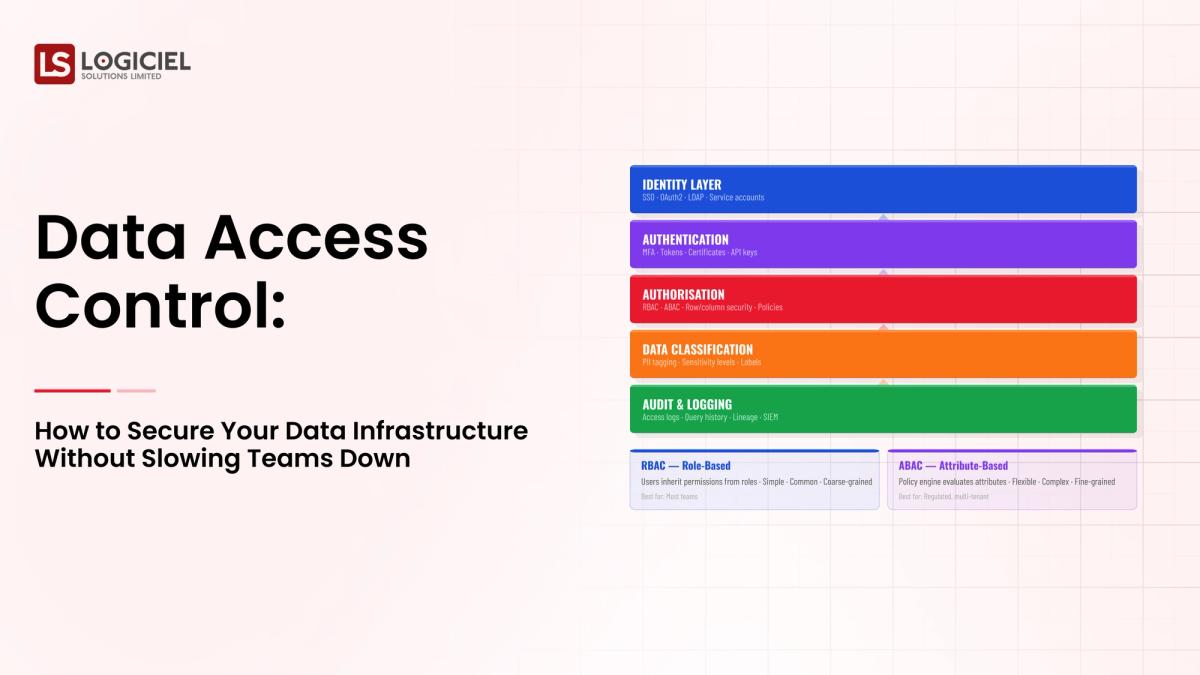
Phase Two: Design the Target Architecture
Now that you have defined how access control should work, you can build the framework in which to help you reach these goals.
1. Define Your Principles.
The security model for your data infrastructure should be:
a. Least-Privilege.
b. Role-Based.
c. Auditable.
d. Scalable.
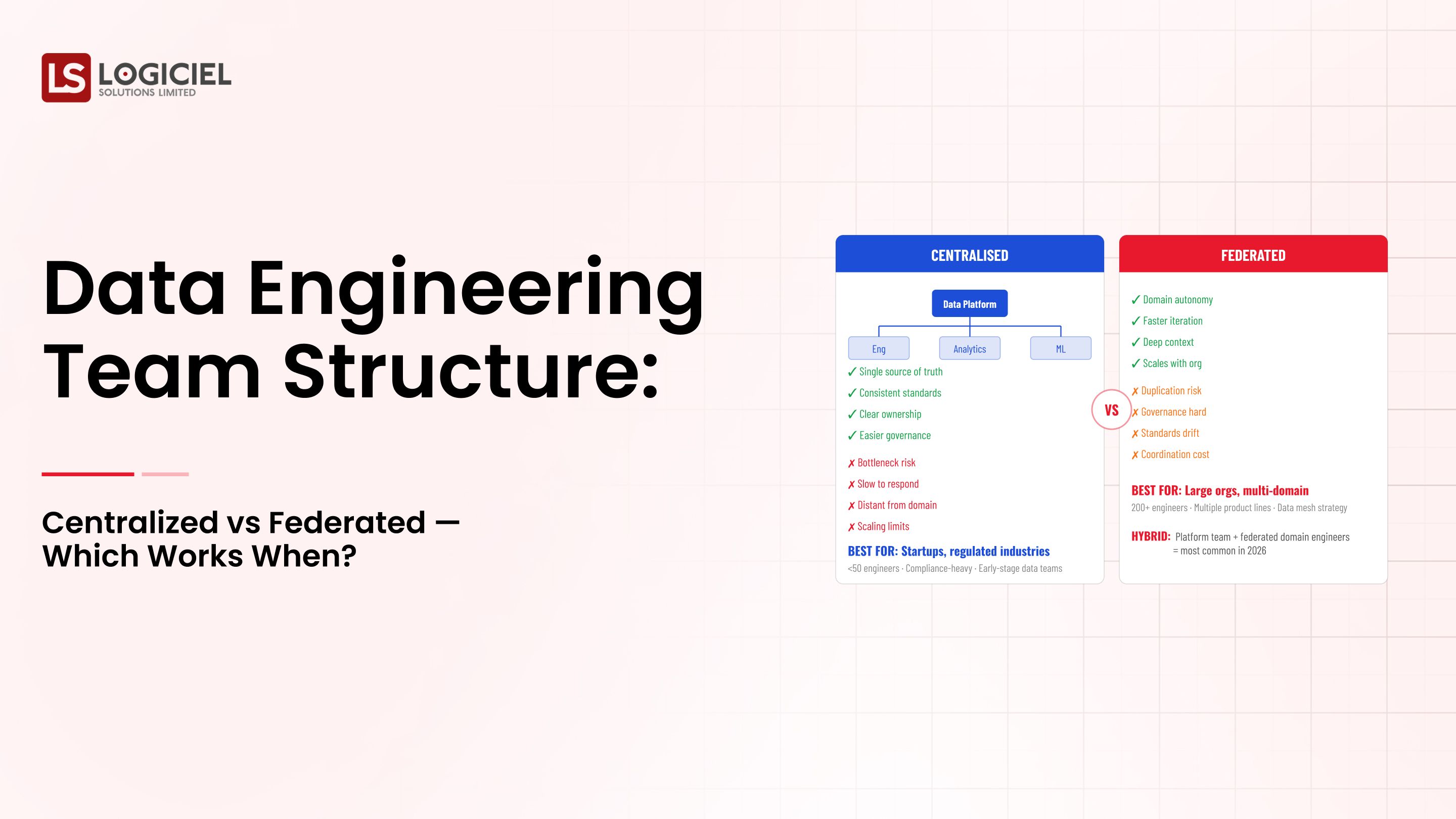
2. Select The Right Model
Common Models Include:
a. Role-Based Access Control (RBAC).
b. Attribute-Based Access Control (ABAC).
Choose a Model Based On:
a. Complexity.
b. Size.
3. Demonstrate Observability
Record:
- Access Log
- Usage Patterns.
- Anomalies.
4. Automate Access Management
Include:
- Auto-Approval Workflows.
- Expiration of Access Privilege.
- User Self-Service Access Requests.
5. Document Policies
Ensure there are:
- Clear Guidelines.
- Consistency in Enforcement.
Key Insight:
Access Control Should Be Automated and Observable Rather Than Manual and Opaque.
Phase Three: Build, Test and Incrementally Rollout
Do Not Attempt A Company-Wide Rollout.
1. Start With One Domain.
Choose:
a. Finance.
b. Customers.
2. Test Your Access Workflows.
Validate:
a. Approval Speed.
Once access is established, you must determine how to secure it.
Access to and from your organization must always be monitored and improved upon. The best way to manage it is to:
1. Establish SLO’s (service-level objectives)
For example an SLO could be:
Requests for access to data must be approved or rejected within one hour after request
There must not be any unauthorized attempts to access data.
2. Create Dashboards
Dashboards can provide visibility into the actual current volumes of requests for access and continued approval/disapproval of those requests. In addition, charts should be established to provide the current statistics of how many security incidents are related to the access of data.
3. Conduct Regular Reviews
You should establish a schedule for regular intervals of reviewing the effectiveness of your access control policies. In addition, periodically review the feedback received from users relative to their experience accessing data.
4. Measure the Business Impact of Access Control
The business impact can be measured by determining how much efficiency (in terms of time) is gained through providing faster access to data (through access controls). Also the reduction of delay and increase of compliance with industry standards can be valid measures of access control.
5. Utilize Intelligent Platforms
Intelligent platforms (like Logiciel) can be used to automate your access control workflows, which can provide greater visibility of your asset data while establishing a unified governance model around data.
Measurement is the key to your organization’s security of the data you access and the systems your data resides in.
All organizations should be able to provide a secure infrastructure for their users; however, if your organization does not have intelligent technology that automates workflows and increases visibility, then the organization’s infrastructure may not provide the security needed to secure its access.
Continuous evaluation of variable factors related to accessing data and providing an environment where employees can access their data in a timely and secure manner, is vital for the successful implementation of access control.
When access control is implemented in the proper manner, organizations will be able to:
- Access their data in a secure manner
- Produce their engineering items at a higher velocity
- Maintain higher compliance.
From Data Chaos to Data Confidence
Inside a 6-month plan that turned 47 fragile pipelines into 98.7% reliability.
Call to Action
To implement access control into your organization:
If you are having difficulties implementing access control within the context of your data infrastructure, you may wish to review the following two resources:
- Why Your Data Infrastructure Continues to Fail.
- How to Evaluate Vendors to Identify the Best Value for Your Organization – 40 Great Questions to Ask Any Vendor You Are Negotiating with for Your Data Infrastructure Purchase
If your organization is looking for assistance with improving your data access control, please contact Logiciel Solutions to schedule an audit of your data access control system.
At Logiciel Solutions we help our clients in the Design and Implementation of secure, scalable, and high-performance data infrastructures by:
- Securing sensitive data regardless of its source and type.
- Providing access to business critical information as quickly as possible.
- Achieving the least amount of operating cost.
Frequently Asked Questions
What is Data Access Control
Data Access Control is simply a process for managing how individuals interact with an organization’s data and what actions are permitted to be performed on that data.
Why is Data Access Control Necessary?
Data Access Control is essential for an organization to secure its data and ensure that only authorized users may access it. Data Access Control also enables employees to be productive without violating any Federal regulations.
What is the Difference Between Role Based Access Control and Attribute-Based Access Control?
Role Based Access Control (RBAC) restricts access to resources based upon the user’s established role. Attribute-Based Access Control (ABAC) restricts access to resources based upon a user’s attributes such as geographic location or the characteristics of the resource being accessed.
Can Organizations Strike a Balance Between Security and the Speed of Data Access?
By employing workflow automation and self-service systems and having well defined policies to minimize any delays, organizations can provide users with quick/efficient access to critical data.
Where Do I Start with Implementing Data Access Control?
Begin by analyzing the patterns of access by users, defining gaps in existing access control mechanisms, and implementing incremental processes or methods of access controls to establish an effective Data Access Control system.